What ever happened to Google’s “Don’t be Evil”? Oh, they deleted it which is a tell they are going to be evil. I think this is part of the larger scheme coordinated with age verification laws and lawsuits, all to make the internet a pain to use so you’ll accept digital ID, eventually requiring an AI agent on your machines to keep tabs on you. And when you’re identified, Tor and VPNs won’t really matter anymore, because nobody will have privacy or anonymity. And Mexico will soon make you biometrically identify yourself for a phone number, with the FCC recently calling for government ID uploading for a phone number. They’re really ramping up for the Mark of the Beast system, and it is a worldwide coordinated effort that shows the world is run by the OCGFC, Owners and Controllers of Global Financialized Capital, and you know who they report to, the soon to be revealed Antichrist.
https://reclaimthenet.org/google-fraud-defense-web-attestation

Google asked permission to gate the open web in 2023, got rejected, and just shipped the same thing as a product update nobody voted on.
By Rick Findlay
In 2023, Google proposed something called Web Environment Integrity. The idea was that websites could check whether your browser was running on Google-certified hardware before letting you in. Mozilla opposed it.
Brave said it would never ship the feature. Vivaldi warned that “any browser choosing not to implement this would not be trusted, and any website using this API could therefore reject users from those browsers.”
Google withdrew the proposal within months. The public won.
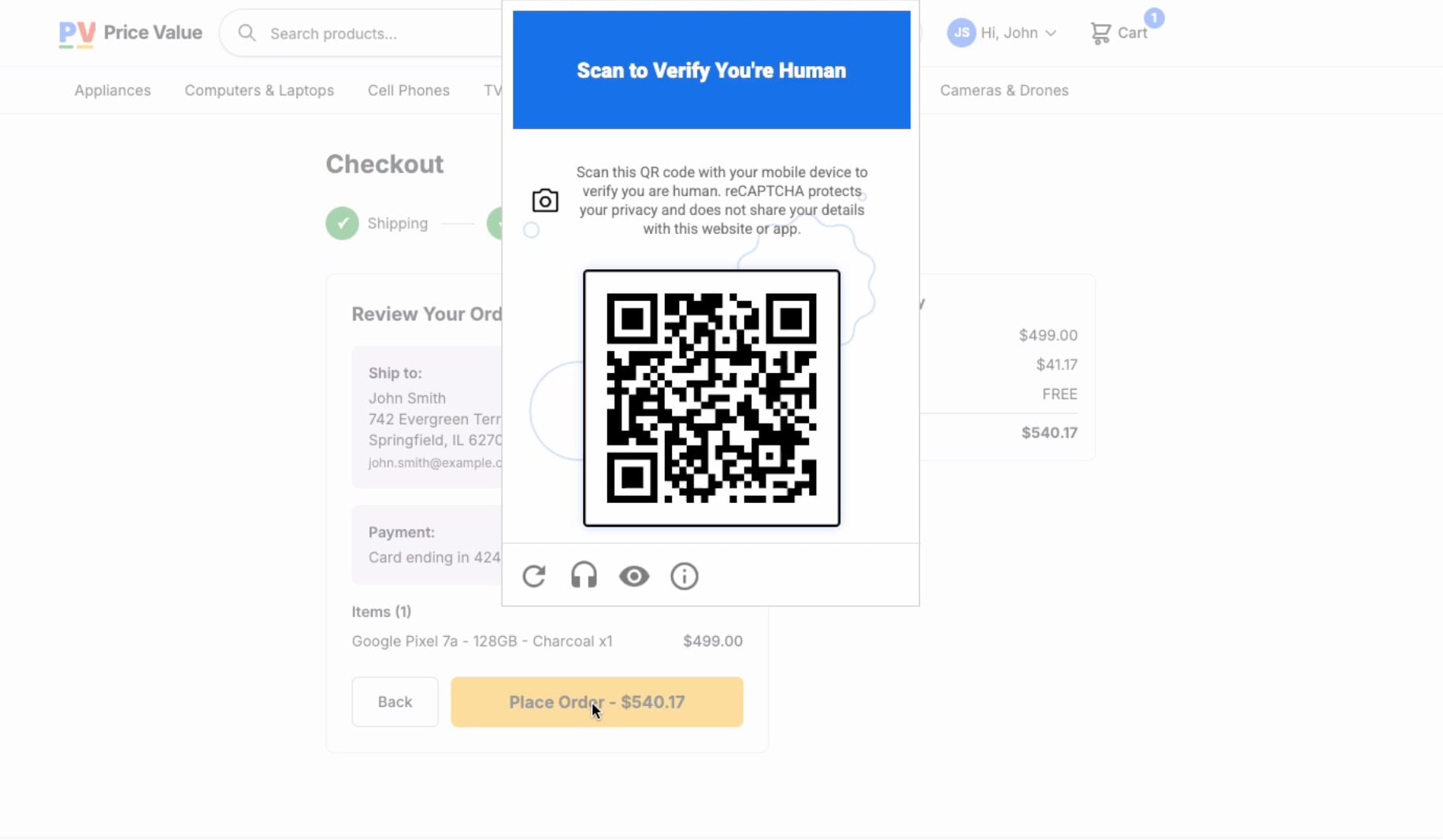
Three years later, though, at Cloud Next ’26, Google announced Fraud Defense, billed as the next evolution of reCAPTCHA. It uses the same Play Integrity API. It requires the same Google-certified hardware and it performs the same device attestation. The difference is that Google didn’t ask anybody this time. There was no standards process or public review. The requirements page just went live and Fraud Defense shipped through reCAPTCHA’s existing install base of more than 14 million domains.
The standards process that killed WEI existed for a specific reason, which was to prevent a single company from deciding who gets to use the open web. Google found a workaround. It launched the same mechanism as a commercial product.
How reCAPTCHA Already Punishes You for Not Being a Google Customer
The scoring has been rigged for years. reCAPTCHA v3 assigns every visitor a risk score between 0.0 and 1.0. Technology consultants who tested the system found that browsers logged into a Google account consistently received low-risk scores, while the same sites visited through Tor or a VPN got flagged as high risk.
Being logged into Google, handing your browsing data to the company’s tracking apparatus, is treated as evidence that you’re human. Protecting your privacy is treated as evidence that you might be a bot.
Anyone who’s used a VPN has experienced this firsthand. Stay logged into your Google account and reCAPTCHA waves you through with a single click, or no challenge at all. Log out, switch to Firefox, enable a tracker blocker, and the puzzles start. They loop. They get harder. Sometimes they never resolve.
VPN users face something even worse because VPN server IP addresses are shared by thousands of people. The behavior of a few users poisons the reputation of the entire address. Low-reputation VPN IPs trigger CAPTCHA rates between 80 and 100 percent, with harder puzzles on top of that.
Privacy extensions like uBlock Origin and Privacy Badger can interfere with reCAPTCHA scripts entirely. The result is infinite challenge loops where verification becomes impossible, no matter how many crosswalks you correctly identify.
reCAPTCHA difficulty scales inversely with how much Google knows about you. That’s the system working as designed.
The People This Actually Hurts
Researchers who scanned the entire IPv4 address space found that 1.3 million websites refuse connections from known Tor exit nodes. Around 3.67 percent of the top 1,000 websites block Tor users at the application level. The researchers concluded that Tor users are “effectively being relegated to the role of second-class citizens on the Internet.”
Tor’s own documentation acknowledges the problem. Websites interpret shared exit relay traffic as suspicious, hitting users with CAPTCHAs, temporary blocks, or warnings about infected traffic. None of which reflects anything the individual user has actually done.
The people who rely on Tor most are journalists working under hostile governments, dissidents, and domestic abuse survivors trying to communicate without being tracked. Anonymous communication is a lifeline for people whose internet access is controlled by states that would harm them for using it freely. CAPTCHA systems treat them identically to automated botnets.
Fraud Defense makes this worse. Google’s requirements page specifies what hardware qualifies for the new QR code challenge. Android phones need Google Play Services version 25.41.30 or greater.
That requirement excludes every de-Googled Android device. GrapheneOS, the security-hardened fork used by privacy enthusiasts, cannot satisfy Play Integrity checks at the level Fraud Defense demands. LineageOS, CalyxOS, and any custom ROM that strips out Google’s proprietary software layer fail for the same reason.
Firefox for Android does not appear in Google’s browser support list. Mozilla’s position on device attestation was stated clearly in 2023 and has not changed. Users of the most privacy-respecting major mobile browser are excluded from verified access by default.
Meanwhile, iOS users pass without installing any Google software. If the requirement were actually about security, Apple’s approach proves device attestation works without Google’s proprietary stack. The fact that Android users specifically need Google Play Services tells you where the real requirement lies.
The Hierarchy
The system Google has built creates an access hierarchy for the web and it’s worth spelling out who sits where.
At the top are users logged into Google accounts, browsing in Chrome on a residential IP. They almost never see CAPTCHAs. Below them sit ordinary users who get occasional puzzles, minor friction, and standard image grids. Below them are VPN users, facing constant challenges because their shared IP addresses are permanently flagged.
Users report multiple CAPTCHAs per session as a baseline. At the bottom sit people running Tor, de-Googled phones, Firefox with anti-fingerprinting settings, or browsers configured to reject tracking cookies.
For these users, the experience ranges from infinite CAPTCHA loops to outright blocks. With Fraud Defense deployed, it becomes total exclusion from sites that use it.
Privacy is penalized and surrendering your data is rewarded with frictionless access. The old system punished privacy-conscious users with harder puzzles. Fraud Defense can lock them out entirely.
The Surveillance Part Google Doesn’t Talk About
The Fraud Defense challenges that resolve successfully transmit a signal to Google. This certified device accessed this site at this time. A device with a stable hardware identity generates a persistent identifier that survives session boundaries, browser switches, and private browsing modes. The company deciding which hardware is legitimate also accumulates a running log of where that hardware goes on the open web.
This sits on top of data harvesting reCAPTCHA was already doing. The French data protection authority, CNIL, found that reCAPTCHA collects IP addresses, cookies Google deposited on the device over the previous six months and a list of browser plugins, and that this data serves purposes beyond security.
Google’s own terms of use tell companies deploying reCAPTCHA that the system collects hardware and software information and transmits it to Google for analysis, and that it is their responsibility to inform users and obtain consent.
reCAPTCHA also sets persistent cookies that enable cross-site tracking. Under the ePrivacy Directive and GDPR, these require explicit prior consent. If a user declines cookies, the reCAPTCHA script is not supposed to load, which breaks form functionality on any site using it. Users are forced to trade privacy for access, a consent mechanism that fails the GDPR’s requirement that consent be freely given.
The QR code mechanism adds hardware-level device identification on top of all of this. The system that verifies you are human also verifies your device, your location, and your identity to an advertising company.
The Bot Problem Fraud Defense Doesn’t Solve
Bot operators can point a camera at a screen to scan the QR code. That is trivial automation with off-the-shelf hardware. A Play Integrity-compliant Android phone costs about $30. For a professional bot farm buying devices in bulk, that is negligible overhead.
The people Fraud Defense actually excludes are privacy-conscious users, de-Googled phone owners, Tor users, and people in countries with repressive governments. These are the populations least likely to be running botnets. The actual bot operators absorb the cost and keep going.
There’s a separate problem that has nothing to do with bots. Security professionals have raised concerns about users being unable to distinguish a legitimate Google CAPTCHA QR code from a phishing QR code. The system trains people to scan codes reflexively to access websites. QR-code phishing attacks have already more than doubled in early 2026. Google built a system that makes phishing easier while failing to stop the bots it was supposedly designed for.
Europe Already Knows
The CNIL ruled that reCAPTCHA enables analysis by Google beyond securing authentication and fined companies for deploying it without proper consent. The Bavarian State Office for Data Protection Supervision found that Google’s lack of transparency about what data reCAPTCHA actually collects makes privacy compliance effectively impossible, because website operators cannot inform users about processing they don’t fully understand themselves.
Data transfers to US servers conflict with the Schrems II ruling. Multiple European authorities, in France, Austria, and Bavaria, have taken enforcement action against reCAPTCHA deployments.
Google’s response, announced in April 2026, was to move to data processor status, which nominally gives organizations control over user data. But the data still flows through Google’s infrastructure. Website operators now bear GDPR compliance responsibility for a system whose data practices they cannot fully audit. Google moved the legal risk to its customers and changed nothing about the pipeline.
The Alternatives Nobody Uses
Cloudflare Turnstile runs invisible verification with no device attestation and no Google dependency. It uses Private Access Tokens, collaborating with device manufacturers to validate devices without collecting or storing the data itself. It is free.
Proof-of-work systems like Friendly Captcha and ALTCHA issue cryptographic challenges where computational cost scales with volume. One human pays a negligible cost. Bot farms running concurrent sessions face exponentially increasing compute expenses. No hardware identifier is transmitted and no certification layer determines who gets access.
These systems prove you are human without requiring you to identify yourself or your device to an advertising company. The difference from Fraud Defense is categorical.
Adoption remains slow for the obvious reason. reCAPTCHA commands roughly 85 percent of the CAPTCHA market and is embedded on more than five million websites. Web developers keep deploying reCAPTCHA because it is the default, because it integrates with Google’s wider ecosystem of Ads, Analytics, and Cloud, and because switching feels risky even when the alternatives are technically and legally superior.
The Pattern
AMP controlled content distribution, privacy Sandbox controls ad targeting, fraud defense controls who is allowed on the web at all. All of these products extend Google’s role as gatekeeper over progressively larger portions of the internet’s basic functionality.
Vivaldi’s 2023 warning has aged well. If attestation became standard, “any browser choosing not to implement this would not be trusted, and any website using this API could therefore reject users from those browsers.”
Google could mandate that sites using Google Ads deploy Fraud Defense, and any non-compliant browser or operating system would be finished.
The web is splitting into attested devices and unattested devices. Privacy-conscious users are being pushed into a second tier where services disappear because they refused to run proprietary software from an advertising company.
The question was never whether the web needs bot protection. Of course it does. The question is whether bot protection requires handing one company a persistent hardware-level identifier for every user on the internet, when alternatives that don’t require that already exist.