A couple things to start with, the Linux Foundation is a captured entity, and not really serving Linux or opensource. And Anthropic saying this AI system is so good at finding chainable exploits, too powerful for the public, is hype. I couldn’t even stomach more than a couple minutes of their video mentioned by Lunduke, as it was so bad in not relaying meaningful information. But as Linux is under attack with IBM, Red Hat trying to kill X.Org for their Wayland windows server for AI hooks, Ubuntu rewriting the coreutils in Rust to change the license and introducing bugs, California, Brazil… demanding age verification be added to opensource operating systems with $7,500 fines per violation… this has got to be another sneaky angle of attack to capture Linux the way Windows, macOS, iOS and Android are captured and being converted into surveillance software without escape. The positive, there will be enough opensource developers to fork projects to keep a free option available for us, but will they prosecute developers like they did with crypto mixer authors? I’d say they’d need to pass new laws, but they prosecute people with no applicable laws in federal courts with captured federal judges that deny defendants putting on a legitimate defense already, so they can deny you a fair trial in federal court as has been exemplified many times when you’re an enemy of the state’s ambitions. So this is very important to pay attention to moving forward.
Regarding the steady creep of operating systems towards surveillance, really desiring agentic AI to be your watchman that reports undesired activity to authorities removing any benefit of encryption, they’re attacking the ways people keep their data protected on their computers highlighted in this story of Microsoft locking the developer accounts for Veracrypt (disk and file encryption) and Wireguard (VPN software). And notice what a joke Microsoft is for these developers to challenge the lockout and get their accounts reinstated, probably only being restored because of the public exposure. It’s time to flee these closed source operating system platforms and their required developer verification programs. And they’ve actually showed a desire to not allow you to install any software on your computer unless it’s signed by an identified developer in their program period, and you see how easily they can lock developers out of the operating system when it suits them. And I wonder if this was something purposeful so the government had more time to utilize exploits on targets… If you run opensource, you don’t need any permission to install software or security updates, and you can compile from source if you desire or its needed for security…
https://www.theregister.com/2026/04/09/microsoft_dev_account_deactivations/
Microsoft locks out VeraCrypt and WireGuard devs, blames verification process
No emails, no warnings, no humans – just bots, catch-22s, and a 60-day appeals queue
Microsoft says that it will work on how it communicates with developers after two leading open source figures were suddenly locked out of their accounts, leaving them unable to sign updates.
Mounir Idrassi and Jason Donenfeld, the developers behind VeraCrypt and WireGuard respectively, both recently reported that Microsoft locked them out of their developer accounts for reasons unknown to them.
Idrassi publicized his experience on March 30, saying: “Microsoft did not send me any emails or prior warnings. I have received no explanation for the termination and their message indicates that no appeal is possible.
“I have tried to contact Microsoft through various channels but I have only received automated replies and bots. I was unable to reach a human.”
Speaking to The Register this week, the developer said that he had still not heard anything from Microsoft.
The lockout affected the developer account associated with IDRIX, the company behind VeraCrypt, which also handles other projects beyond the encryption utility.
“I cannot sign the VeraCrypt driver or the VeraCrypt bootloader through the hardware dashboard,” he said. “This also prevents me from signing drivers and components for my customers on different projects, so this situation impacts my work beyond VeraCrypt.”
It was a similar story for Donenfeld, who also claimed Microsoft had not made him aware of why his account access was revoked.
“No warning at all, no notification,” he wrote on Hacker News. “One day, I sign in to publish an update, and yikes, account suspended.”
He also expressed concerns about cybersecurity. If the WireGuard team became aware of a vulnerability affecting the VPN, he would have no way of signing an update to patch it.
“As somebody on Hacker News noted, if someone was a bad actor, right now would be a pretty good time to start exploiting zero days in WireGuard. I mean, hopefully there aren’t zero days in WireGuard. But if there were, Jiminy Cricket!”
Donenfeld told The Register that his saga began roughly two weeks ago, after spending weeks working on improvements to the WireGuard user application and its kernel driver, including rebuilding the latter’s infrastructure to pass the Windows Hardware Lab Kit (WHLK) test suite, which he described as “a neat project,” but “a massive pain.”
He said: “With the WHLK package ready, I got a new super expensive EV code signing certificate – this Microsoft requirement is kind of a racket in its own right – and I was ready to login to the Partner Portal and submit my signed WHLK package and driver to Microsoft for automated inspection, which usually results in a Microsoft signature required for loading drivers into the kernel.”
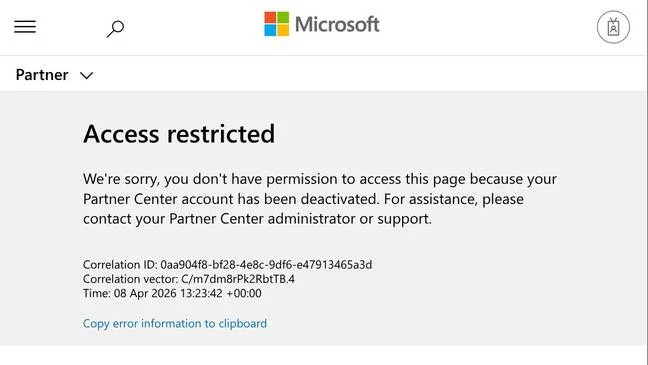
However, he was met with a message saying that his account had been deactivated.
Microsoft’s message to WireGuard’s Jason Donenfeld, informing of his account deactivation
“Microsoft never sent me any notification at all about this,” Donenfeld added. “I’ve looked in every inbox in every spam folder in every mail log, and zero, nothing, zilch.”
The appeals process directed Donenfeld to an AI support ticket tool, but this didn’t allow him to select the workplace to which the appeal pertained because his account was deactivated.
This caused what he called a catch-22 scenario, where he needed to file the appeal to reinstate his account, but he also needed an account to file the appeal.
The workaround he eventually found was to file an appeal via the Azure team for something unrelated, and get them to redirect it to the right team.
“Finally this week, and after bugging some friends who work at Microsoft, and after emailing the authors of those blog posts, some news started to trickle out,” Donenfeld said via email. “They received the appeal. It takes 60 days. No, no amount of pressure or vouching that I am, in fact, a real person with a real project (used by Microsoft themselves, apparently!) will speed it up. Sixty days. No exceptions.
“By the way, they didn’t note what was required for the appeal in terms of documentation, so I just sort of guessed. So, after sixty days, they could just deny it, and I’d be screwed.
“It struck me as contrary to Microsoft’s business interests, so I emailed [Microsoft’s Standards of Business Conduct department]. But they didn’t think it was important enough and referred me to the executive support team instead, who told me yesterday that the right people did, in fact, receive my appeal (I had no prior confirmation), but there was nothing to do to get it processed and no insight into when/how/etc. Totally opaque.”
Microsoft responds
Pavan Davuluri, Microsoft’s President of Windows and Devices, said both Idrassi and Donenfeld should have their accounts restored “soon.”
“We’ve seen these reports and are actively working to resolve this as quickly as possible,” Davuluri Xeeted. “We’ve reached out to VeraCrypt and have spoken to Jason at WireGuard, they should be back up and running soon.”
He explained that both deactivations were executed as part of the Windows Hardware Program’s account verification procedures.
The company published a blog in October, giving devs a two-week warning that if their accounts had not been verified since April 2024, Microsoft would issue mandatory account verification notifications.
“We worked hard to make sure partners understood this was coming, from emails, banners, reminders,” said Davuluri.
“And we know that sometimes things still get missed. We’re taking this as an opportunity to review how we communicate changes like this and make sure we’re doing it better.”
For anyone else looking for help with reinstating their accounts, it’s Copilot to the rescue. Davuluri pointed those in similar boats to a support page outlining the steps they can take.
Since Davuluri’s social media post, Donenfeld confirmed to The Register that his account was reinstated and he was able to get his kernel driver update out as of Thursday morning.