UPDATE: As more news has come out about how Tor is dragging their feet fixing certain issues as if they’re trying to assist governments and law enforcement in being able to deanonymize targets, there was a interesting post on the darknet about trusting Tor. Consequently, it’s a good time to revisit this post at the bottom about how you can filter out Tor nodes from Germany and the Netherlands. And this is something you can do in the Tor Browser, or with Tor on a machine with hidden services, e.g. Bitcoin and Lightning Nodes… And to use these darknet Tor hidden service links below, you’ll need to load them into the Tor Browser (and I’d make sure JavaScript is off before looking around the darknet).
http://opbible7nans45sg33cbyeiwqmlp5fu7lklu6jd6f3mivrjeqadco5yd.onion//opsec/torhoneypot/
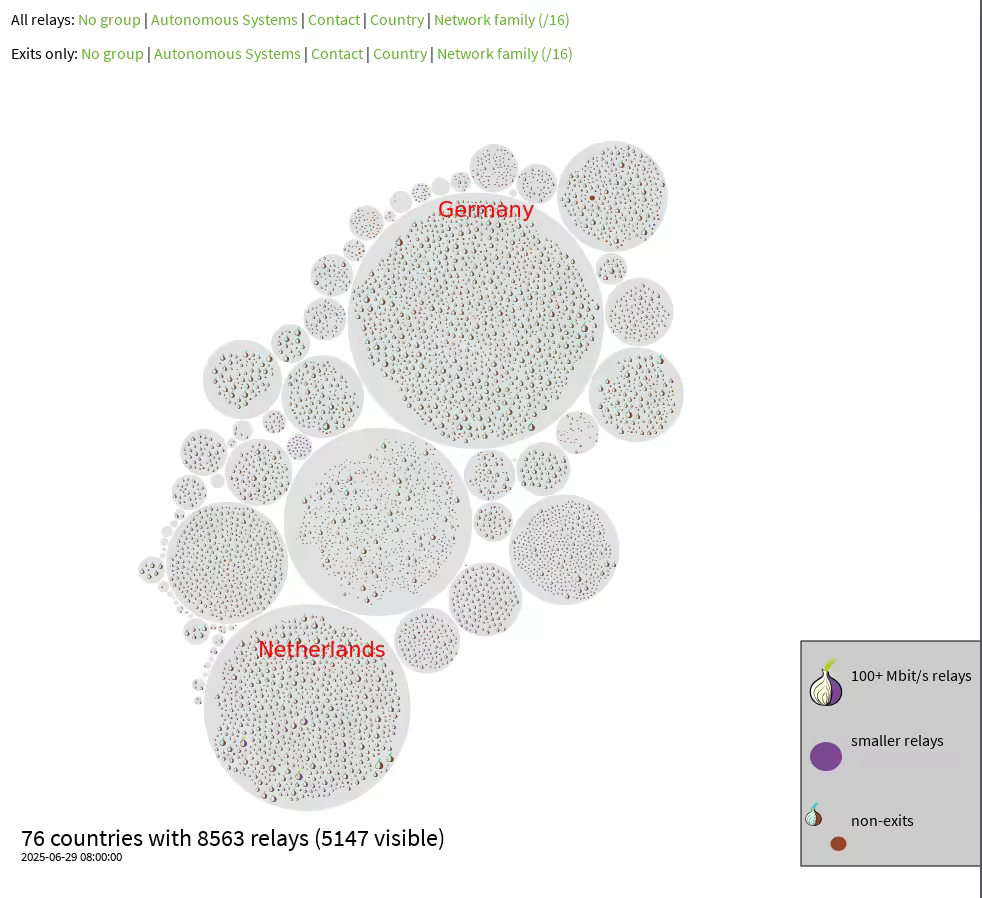
I had done some searches because I had noticed the German Tor Node problem, but leave it to the OPSEC Bible to have a blog post on the issue. I’ve never noticed too many Netherlands Tor Nodes, but I would see them regularly enough, so worth including as well. Consequently, the article linked below on the Darknet is a good article with differing levels of speculation, and I’ve included how you can exclude Tor Nodes from these two countries. I highly recommend the whole article which also has a lot of graphics and why I didn’t reproduce it in full. Also, I had mentioned issues I was having with with sites slowly not loading all the way or at all, and needing to changed circuits, and if these are malicious nodes trying to implement some type of timing attack that would seem to fit. My solution was to run my own Entry Bridge Tor Node I control with certificate and fingerprint, which insulated me from the BGP networking attack and also makes sure I use an entry point into Tor I control with proper obfuscation enabled. Since Tor was working great with my Bridge, I’m deducing the timing attack requires control of the guard (entry) Node. And you’d have to assume that nation states are behind a lot of malicious Tor nodes.
http://blog.nowherejezfoltodf4jiyl6r56jnzintap5vyjlia7fkirfsnfizflqd.onion/opsec/germantornodes/
The Pessimistic solution: What can i do about it ?
By tweaking your Tor torrc configuration, you can make sure that your tor circuits do not go through either Germany or Netherlands, by doing the following steps:
On both the clientside and the serverside you can edit your torrc config file to have the following lines:
[ localhost ] [ /dev/pts/7 ] [~]
→ vim /etc/tor/torrc
[ localhost ] [ /dev/pts/7 ] [~]
→ cat /etc/tor/torrc | tail -n3
ExcludeNodes {de},{nl}
ExcludeExitNodes {de},{nl}
StrictNodes 1
[ localhost ] [ /dev/pts/7 ] [~]
→ systemctl restart tor@daemon
On the tor browser side, you can edit the torrc configuration as follows:
[ localhost ] [ /dev/pts/6 ] [~]
→ vim ~/.tb/tor-browser/Browser/TorBrowser/Data/Tor/torrc-defaults
[ localhost ] [ /dev/pts/6 ] [~]
→ cat ~/.tb/tor-browser/Browser/TorBrowser/Data/Tor/torrc-defaults | tail -n5
[ localhost ] [ /dev/pts/6 ] [~]
→ cat ~/.tb/tor-browser/Browser/TorBrowser/Data/Tor/torrc-defaults | tail -n4
ExcludeNodes {de},{nl}
ExcludeExitNodes {de},{nl}
StrictNodes 1
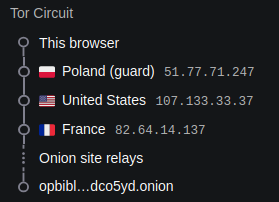
Then simply restart the Tor browser by hitting Ctrl+Q and then re-launch it, Then check if your tor circuits are going through those 2 countries or not: